There will be 26-30 billion connected devices by 2020! Need to worry about confidentiality, integrity and availability - but is that enough? Is there something more important than keeping your credentials safe? Yes - safety! Many of these devices are controlling environmental factors in laboratories, chemical mixtures, etc.
Rios and Butts looked at devices connected to the internet, in a public space accessible to the general public, and exploitation of the device could result in a safety issue.
Currently, there are only a few devices that meet all 3 criteria. One surprising device they found - car washes! The looked at Laserwash. Car washes are really just industrial control systems (ICS) - and come with all the attitude and controls those systems come with. The car wash is different than most ICSs - it's accessible to the general public, with no screening at all.
The researchers wrote an exploit that can cause a car wash system to physically attack an occupant. Currently there is no patch for the vulnerability - if you own one of these car washes, please contact the manufacturer.
The big takeaway here - you should wear a hard hat to go into a car wash.
When Charlie and Chris attacked a car, they had to buy a car and about $15,000 in tools to analyze the car. The systems are so specialized you must buy specialized tools. In that referenced paper, the tools they bought were only good for Fiat-Chrysler vehicles.
Their cost considerations - acquired firmware in 2014 through compensated operator. Did not find a willing owner until 2017 (which they also had to compensate and pay for the car washes). Buying a carwash is a large sum ($250K?) - so they really had to find people that already owned them that were interested in the academic interest. shouldn't there be a better way? Should manufacturers give access to systems? Without this, researchers are looking at live and deployed systems and spending their own money.
Initially disclosed the bug to vendor in February 2015. Reached out repeatedely through April 2017... still no response. In May they got a fully working remote exploit code (PoC) - still no response. Once posted to BlackHat schedule, vendor asked if they tested against a demo system.
From other vendors, got a lot of comments like "that's not how we designed the system to work", etc. so writing up a vulnerability is not sufficient. Researchers had to do the PoC and prove their exploit worked - very costly and time consuming. Could vendors do better?
Need to remember these devices are just a computer - the car wash has storage, cables, disks, programs. Older car washes had a manual physically connected interface with a joy stick to manually control the arm, etc. Now they have close proximity remotes. If you are within line of site of the car wash, you can control the car wash.

When these car washes are deployed, they likely come with warnings for the new owner that the car wash is connected to the Internet. But, why? You can configure the car wash to send emails. Maybe the owner wants to see how many car washes happened in any given day, which packages are the most popular and what times are the busiest - business reasons.
But - this car wash is on Facebook, YouTube and LinkedIn. Now, that is perplexing.
At the end of the day, this is a computer running WindowsCE, Intrinsyc Rainbow web server with a Binary Gateway Interface. Windows CE is end of life - there is no more support for any vulnerabilities. The webserver calls mapped to an unmanaged ARM DLLs. There are a lot of DLLs on the system that could be abused.

From the web browser, you can point to various DLLs and access them directly via rbhttp22.dll.
Now... there are credentials. The owner credentials are ...12345. This gives you all access, including free car washes. The engineer creds (PDQENG) are 83340. But, the researchers don't think having the default creds is a true exploit.
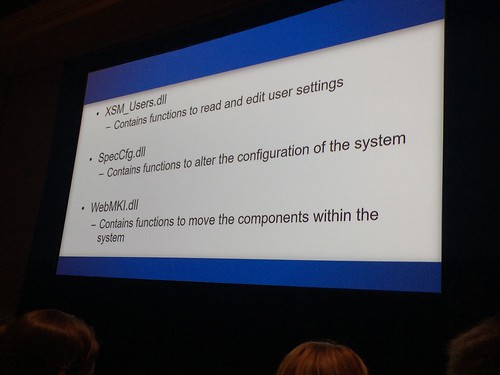
There is a PLC driving the functionality of the car wash. This is a system of systems, lots of communication happening. There are 3 key DLLs for exploits.
They won't be publishing the details of the exploit, because these vulnerabilities are just not fixed.
One of the basic issues is that authentication is handled very simply. The authentication level is set to OWNER before the credentials are checked...Just cause an exception in the authentication routine, and you will remain as OWNER!
It doesn't matter if the owner changes the password, you can read it back.
The researchers identified where the hardware safety mechanisms were - those are difficult to override, much easier to do the software mechanisms. An example of a hardware mechanism si an example of a welded on safety stopper - more difficult to defeat.
Software controls the doors that go up and down, after interacting with sensors that report "all clear". You can exploit the door, for example, to disregard the response from the sensors. Video was shown of a car wash door crushing the hood of a car that was only part way into the car wash.
There is another issue with CVSS scoring. There is a medical infusion device with a vulnerability that can kill the user - it's rated at 7.1. A bug in a medical cabinet that allows people to steal drugs - 9.7. Why should that be "more severe" than death? The speakers have additionally been working on a scoring system specifically for medical devices.
You cannot rely on software solely for physical security, and you should never respond to a vulnerability researcher with "the system wasn't designed to do that" :-)
Update: here's the referenced video:



No comments:
Post a Comment